Accelerate time-to-market
Accelerate developer productivity and empowers teams to deliver unique high-value, complex apps fast.
Empowering businesses to go-to-market faster
Join our clients in saving thousands of dollars per year on dev expenses.
Develop applications 10X faster, ship in clicks
Front-ends.
The MaxBlox no-code platform makes front-ends easy, even if no one on your team has built one before.
Back-ends.
Build your back-end, including APIs, web services, data models, workflows, and business rules in record time.
Automation.
Automate and orchestrate your unique cross-functional workflows, eliminating inefficiency and repetitive tasks.
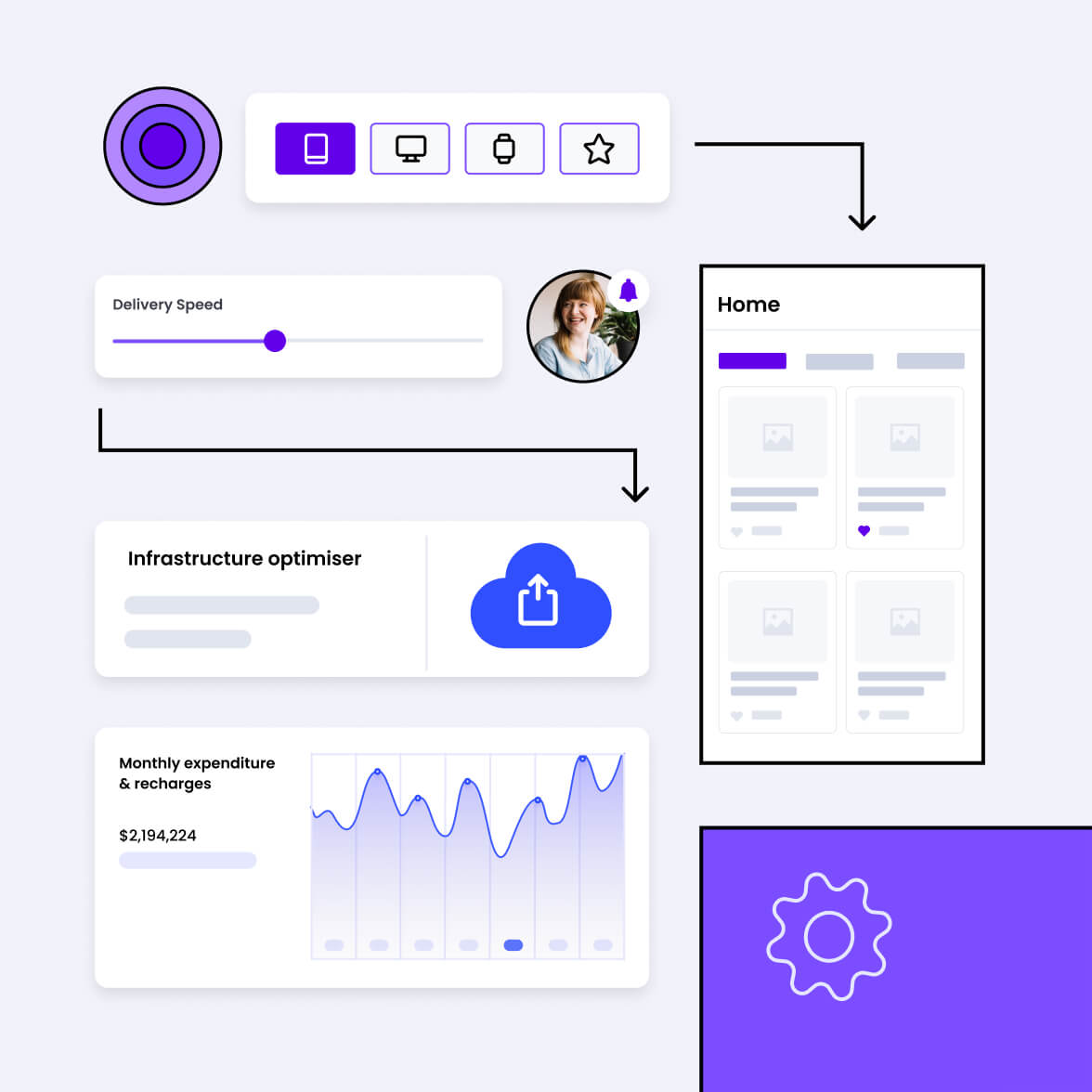
Discover the MaxBlox low-code platform
Build mission-critical apps and update them–fast–with the MaxBlox low-code platform.
Once your data is connected, you can use it anywhere inside your project.
Native integrations for Salesforce, Quickbooks, Dynamics & SQL.
Works with any REST API.
Data in
Think of your apps as data providers. Bring "Data In" and send "Data Out" between your apps and MaxBlox.
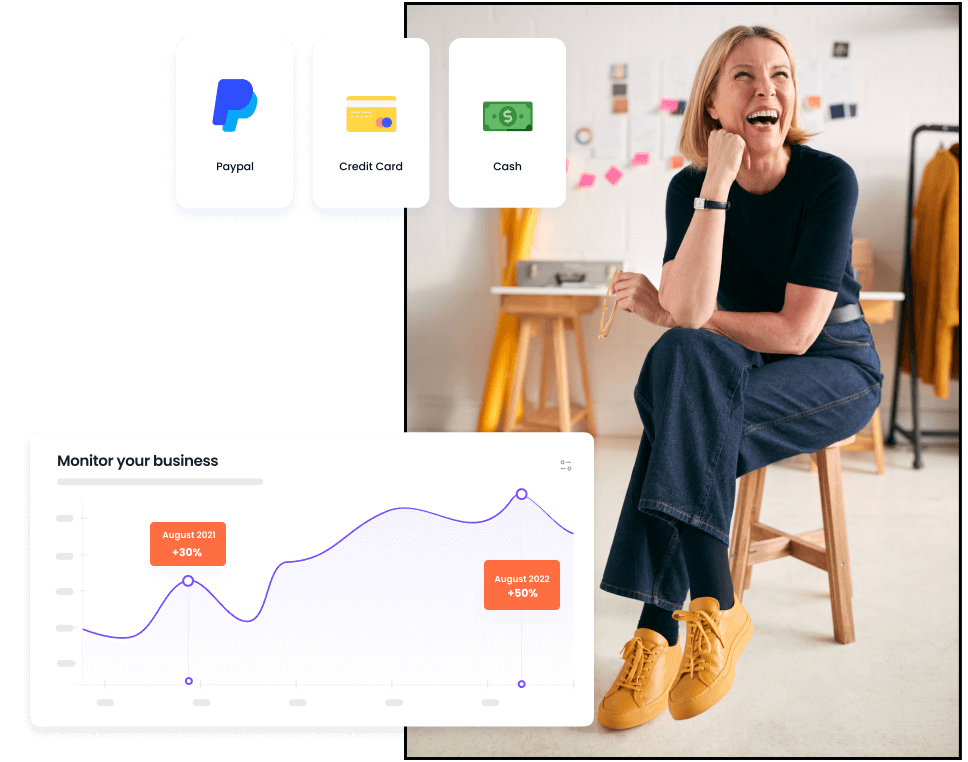
Quickly create and assign workflows to your team.
Use conditional logic to create truly dynamic workflows with if/then logic that adapts to your team's changing needs.
Streamline any process that needs authorization from another person.
Actions
Move work forward faster with no-code workflows that perfectly match your team’s agility and scale.
Quickly create and assign workflows to your team.
Use conditional logic to create truly dynamic workflows with if/then logic that adapts to your team's changing needs.
Streamline any process that needs authorization from another person.
Data out
Move work forward faster with no-code workflows that perfectly match your team’s agility and scale.
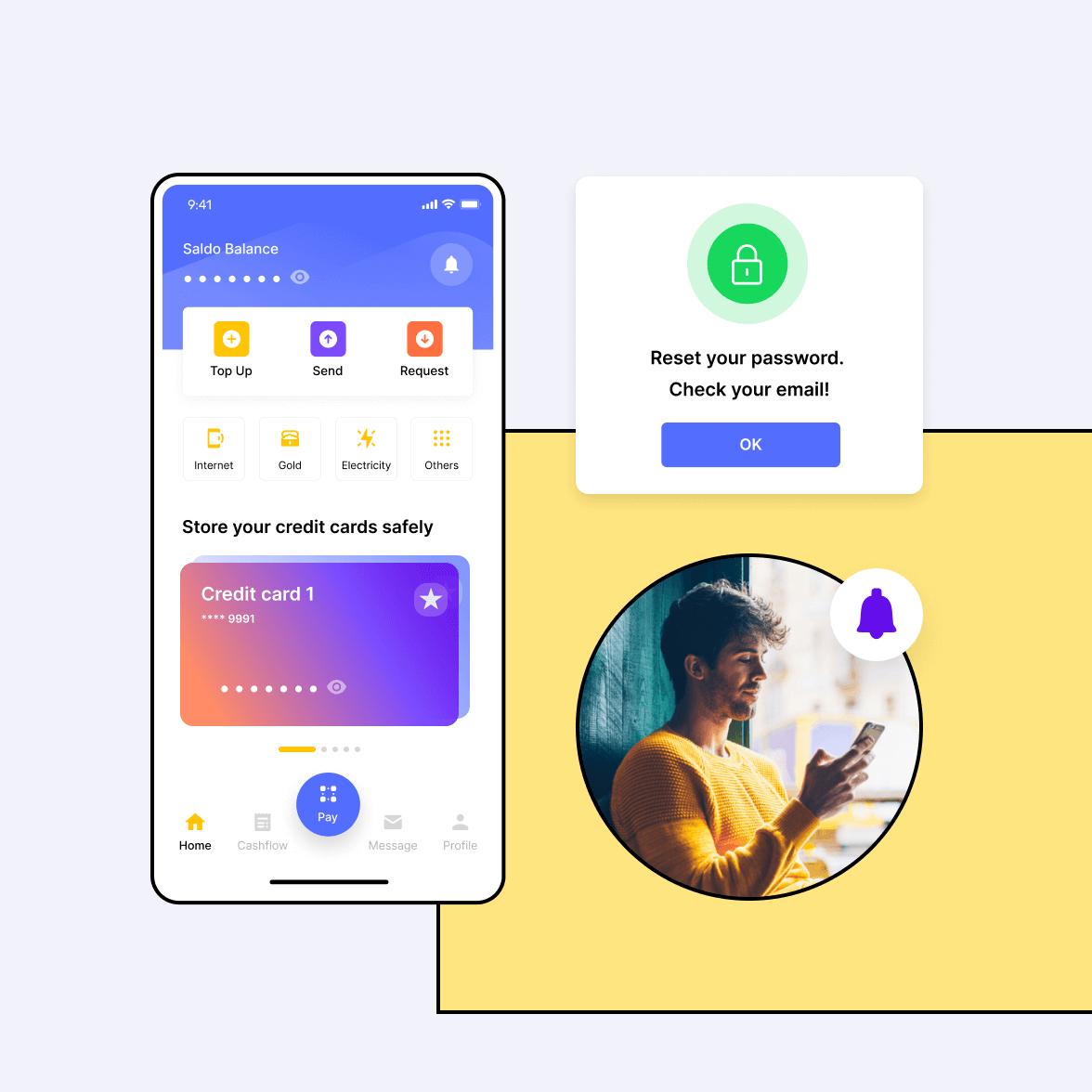
Native authentication layer built for SaaS apps.
Create sign-up, log-in, log-out, and password reset functionality.
Custom authentication providers can be integrated via REST API.
Authentication
User sign-up, log-in, protected content, and Role access without single line of code.
Companies of all sizes trust MaxBlox
Open Source with the security, scalability, and extensibility you need.
Protecting your apps and data with industry best practices.
Stop worrying about GDPR, HIPAA, SOC 2, PCI DSS & ISO 27001. Be compliant from day zero.
Serve millions of users from day zero
MaxBlox runs production-grade apps for many companies and can scale automatically as your app grows in users and complexity.
No limits to what you can do with MaxBlox
If you want functionality that MaxBlox doesn’t natively provide, it’s easy to extend capabilities using custom code.
Build mission-critical apps to the highest quality standard
Deliver high-quality applications for millions of consumers and core enterprise systems that meet all the criteria for mission-critical software with easy integrations, cloud-native scalability, security, resilience, and performance.
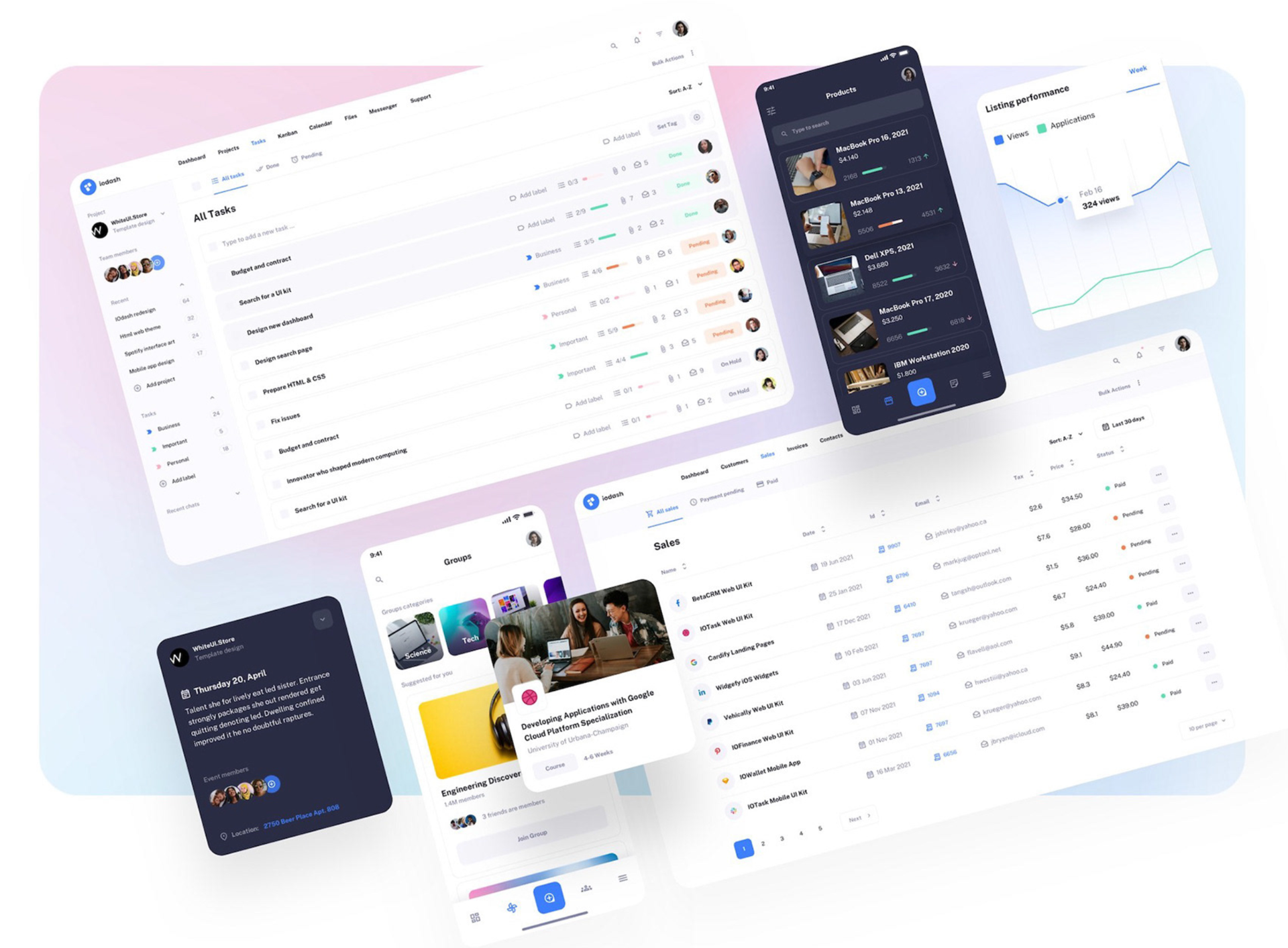
Sales Management
Unify customer and sales data, build custom sales apps and launch reports with ease.
Custom ERP
Why choose monolithic, off-the-shelf ERP software and then spend years and a fortune in customizations?
Project Management
Complete visibility on spending, tasks, timesheets, and more – all from a single platform.
Customer Portals
Dedicated portals for your customers and business partners to interact with your company's applications and data.
Inventory Processing
Manage the availability of raw materials, work in progress, and finished and MRO goods on a single, searchable cloud-based interface.
Customer Experience
Empower your customers and suppliers with a dedicated self-service portal for timely tracking of quotes, orders, and consigned inventory.
Resource Allocation
Stop sifting through hoards of spreadsheets to find the right resources for your projects.
Enterprise Data Solutions
Collect, unify, analyze, share, and manage data from multiple sources seamlessly.
Join 50+ happy businesses that use MaxBlox
I expect to get a return on investment within twelve months of the end of the project. Our lives are getting a lot easier with this solution. I am very happy with the capabilities and professionalism. I have invited them to help us again with the building out of additional functionality to make us completely automated.
Senior Manager
Mercedes Benz Research and Development - North America
Schedule a meeting with MaxBlox
From simple-complex build applications for any use case like:
- Sales Management
- Custom ERP
- Project Management
- Customer Portals
- Inventory Processing
- Customer Experience
- Resource Allocation
- Enterprise Data Solutions

Still wondering if MaxBlox is the right solution for you?
Talk to out App Development experts today!
MaxBlox
Open-source, No-code platform to build software products 10x faster.
Copyright © 2023 MaxBlox, Inc. All rights reserved.
HQ - 80 Cabrillo Hwy Suite Q216, Half Moon Bay, CA 94019 USA